In today’s digital age, protecting sensitive information is crucial for businesses of all sizes. While large enterprises may have extensive resources to invest in robust security measures, smaller businesses often struggle to balance the need for strong information security with budget…
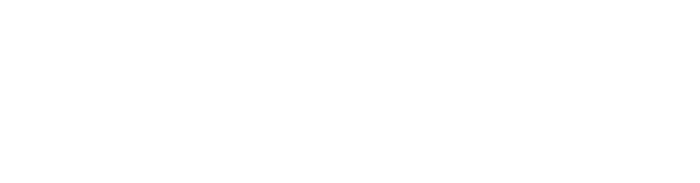
Exploring Mobile App Pen-Testing Methodologies for Secure Mobile App Development
In today’s digital age, healthcare organizations handle vast amounts of sensitive data, from patient medical records to financial information. Protecting this data is not only a legal requirement but also a crucial aspect of maintaining trust and operational integrity. This is…
Understanding ISO 27001 Certification for Healthcare Organizations
In today’s digital age, healthcare organizations handle vast amounts of sensitive data, from patient medical records to financial information. Protecting this data is not only a legal requirement but also a crucial aspect of maintaining trust and operational integrity. This is…
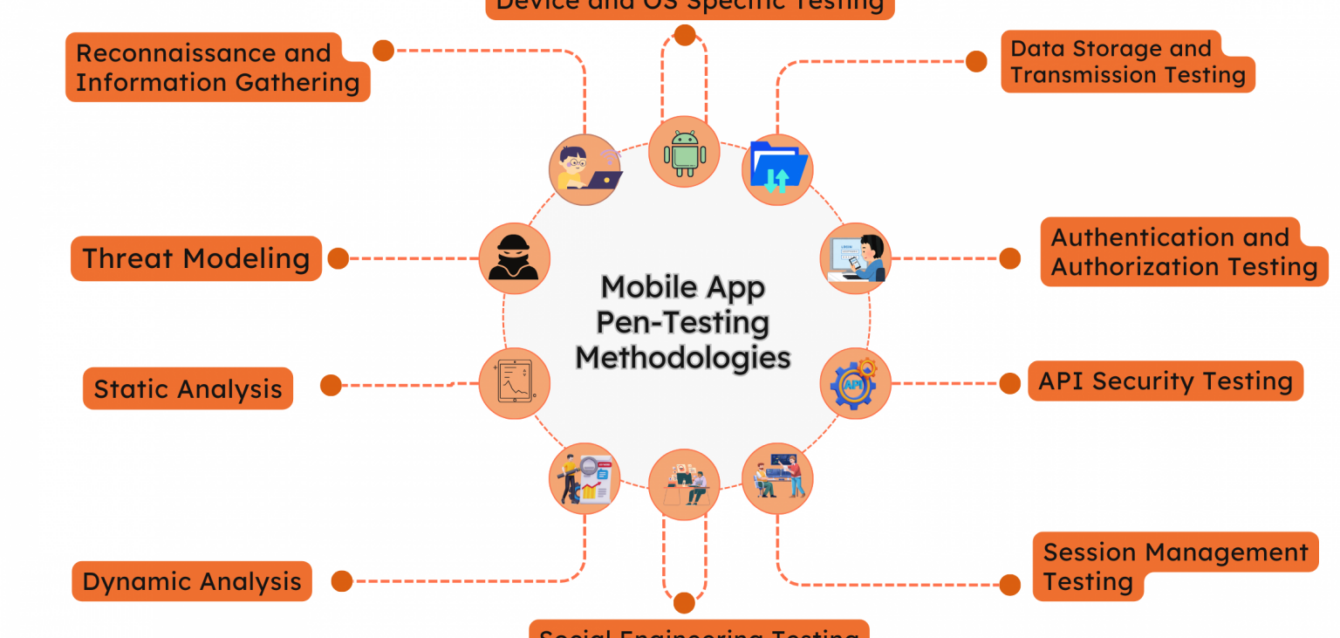
How Network Penetration Testing Works
In today’s digital age, information security services are paramount for businesses to protect their sensitive data and systems from cyber threats. One of the crucial aspects of information security is Network Penetration Testing. This practice involves simulating cyber attacks to identify…
How to Perform Mobile Application Penetration Testing
In today’s digital landscape, mobile applications have become an integral part of our daily lives, facilitating everything from banking to social networking. As their usage increases, so does the need for robust security measures to protect sensitive user data. This is…